Uncontrolled local administrators groups within any organisation pose a huge security risk. Because these groups are locally managed it becomes difficult to audit and maintain them.
Introduction
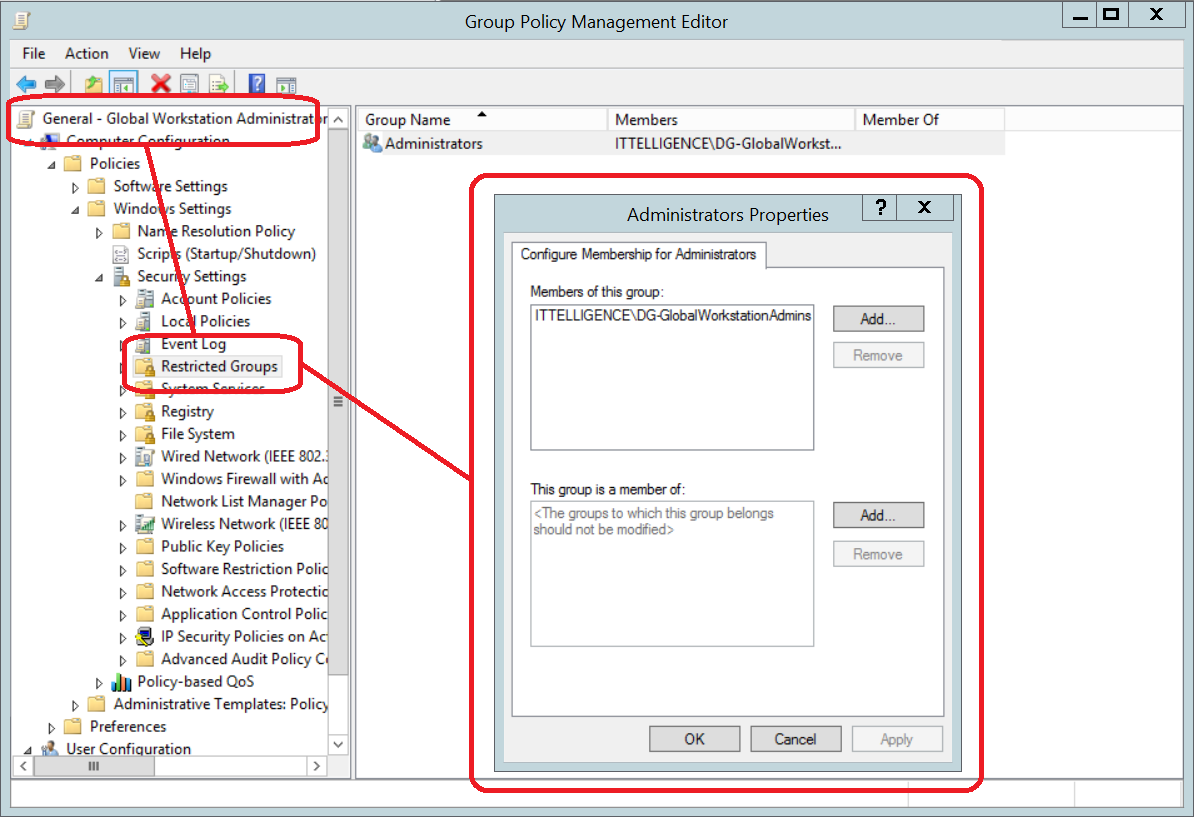
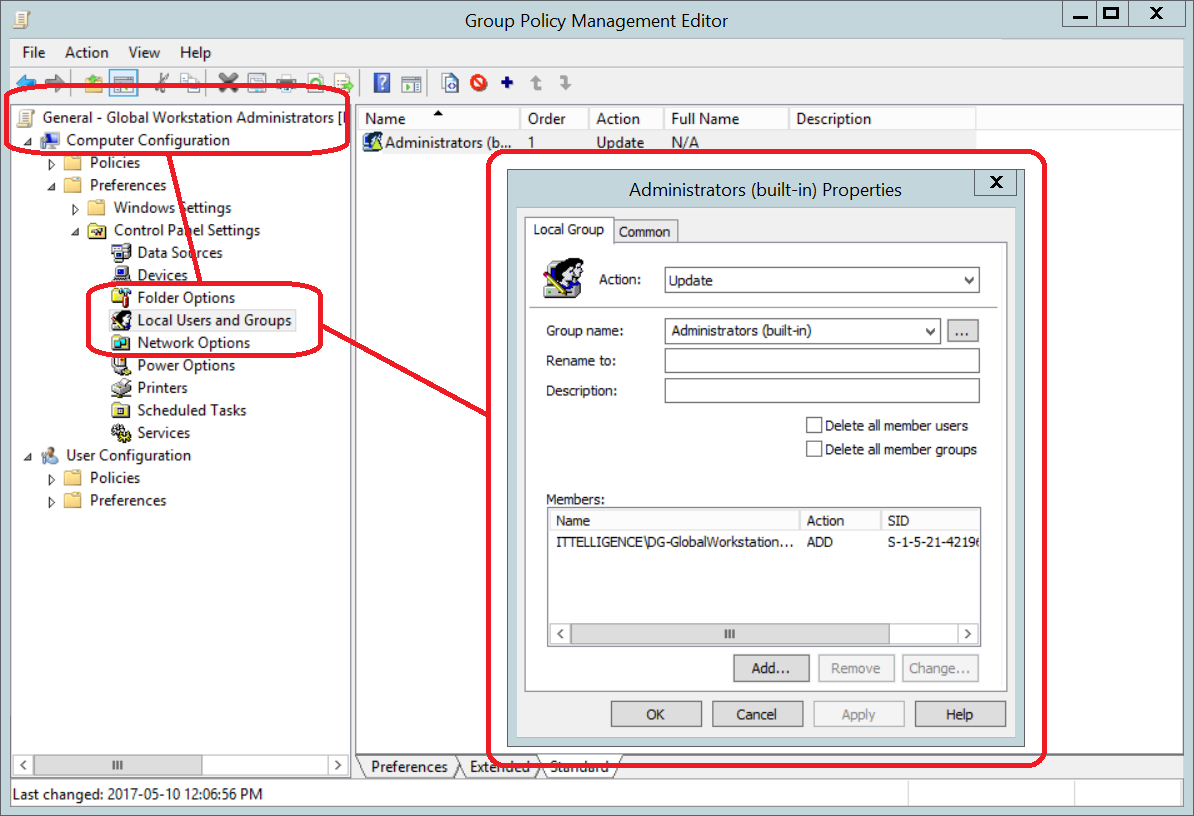
Active Directory does provide mechanisms such as Group Policy Preferences, Restricted Groups etc. which can manage groups centrally. The issue is that local Administrators groups can differ vastly from computer to computer and because of this it is difficult
to standardize settings within a policy. This leads to over permissions because these individual permissions are painful to define and a higher privileged than required is usually assigned.
To make it worse, in a mature environment you first need visibility on current members and chances are that you would need to rely on other parties to rectify or change these because of the initial requirements.
In this article, I explain my approach to centrally manage Local Administrators group from Active Directory using a custom developed application.
Definitions
| Local Administrators group |
The local built-in Administrators group found on each computer. |
| AD Local Admin group |
An Active Directory group for each computer that is added to the Local Administrators group of the computer. Its purpose is to hold all the members intended to have Administrative permission to a particular computer. |
| Local Administrator Permission |
Referring to the actual permissions given to Administrators. |
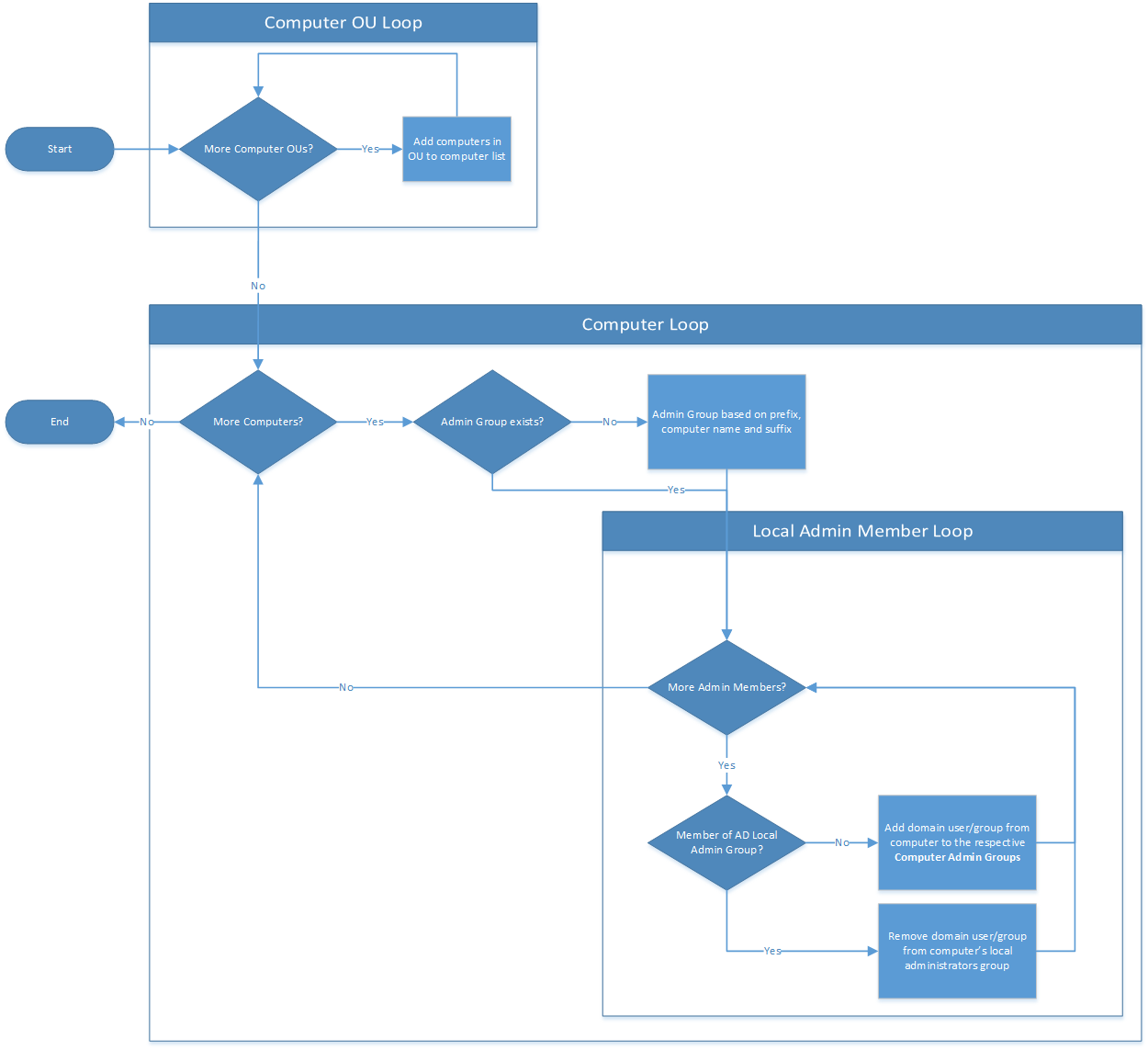
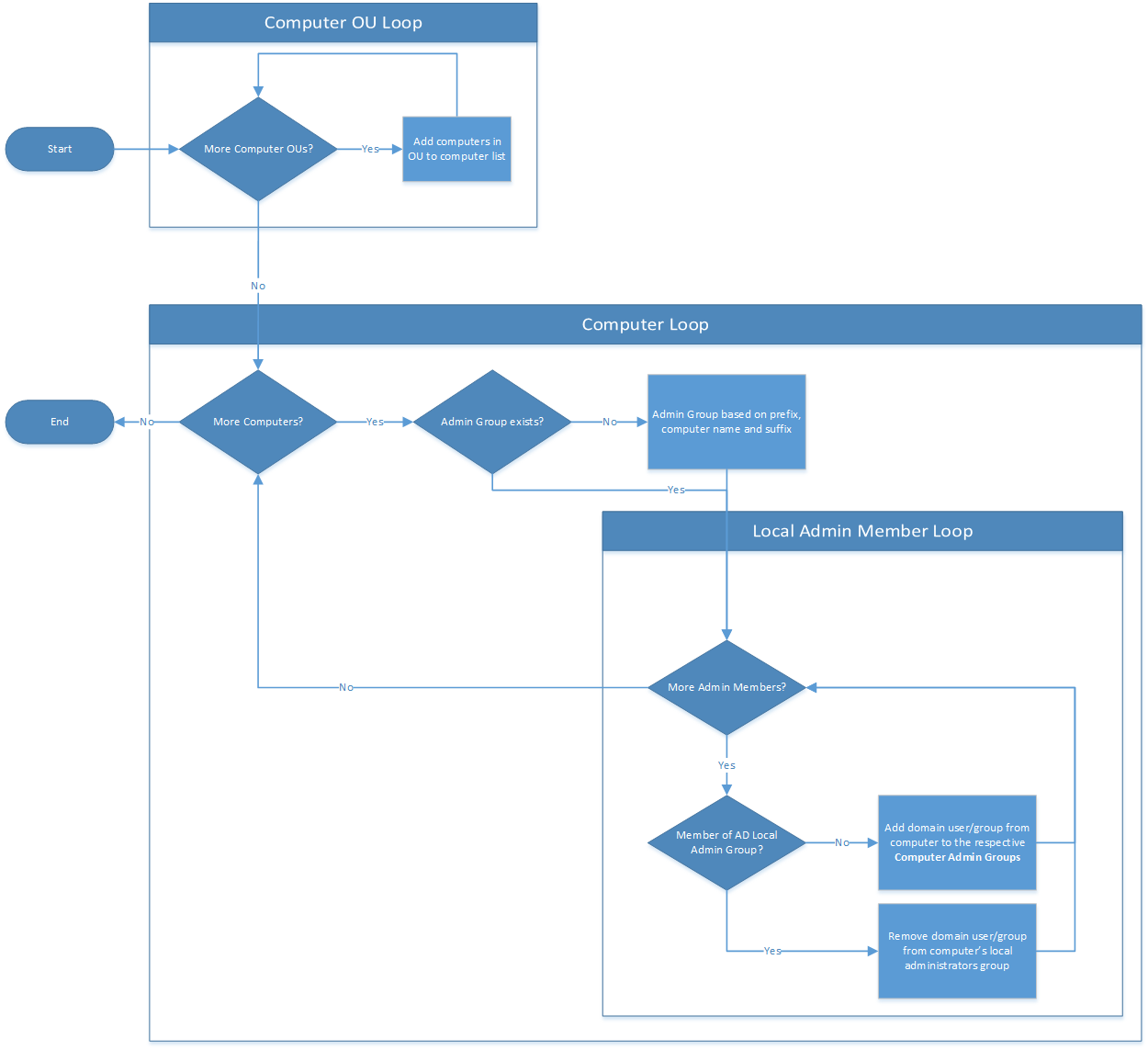
Process Flow
Computer OU Loop
Application enumerates computers in the computer OUs specified and adds them to a collection.
Computer Loop
Creates a computer AD Local Admin group for each computer if it doesn’t already exist.
Local Admin Member Loop
Add members of Local Administrators group to AD Local Admin group. If the member is already part of the AD Local Admin group, remove it from computer’s Local Administrators group. It is important to note that these
two actions will not occur within same execution to allow Kerberos tokens to update.
Benefits
- Rebuilding computers with the same computer name will restore all administrators.
- Enable auditing of users with local Administrators permissions without directly querying computer.
- AD Local Admin group members can be queried directly from Active Directory without connecting to remote computers.
- Enforce a stronger password policy for the user accounts with Administrator permission to certain computers.
- Add required AD Local Admin group to a group defined in a fine-grained password policy
- Remove dormant/orphaned entries.
- Central management of local administrator permissions.
- Simply add users or groups (preferably role groups) to the AD Local Admin group to give local Administrator permissions on computers.
- Any new members will automatically be removed from Local Administrators group and added to the AD LocalAdmins group
- After implementation, local administrator permission can be enforced via AD.
Implementation
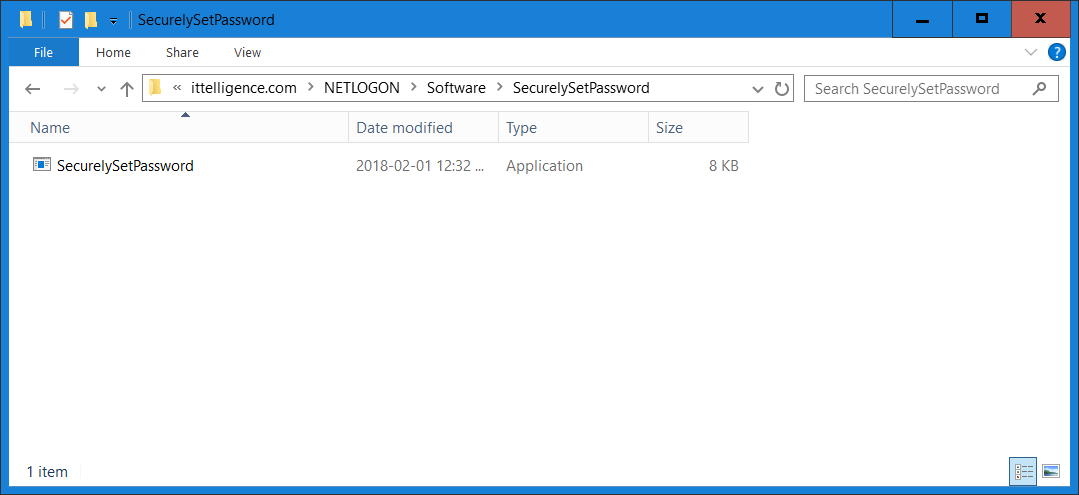
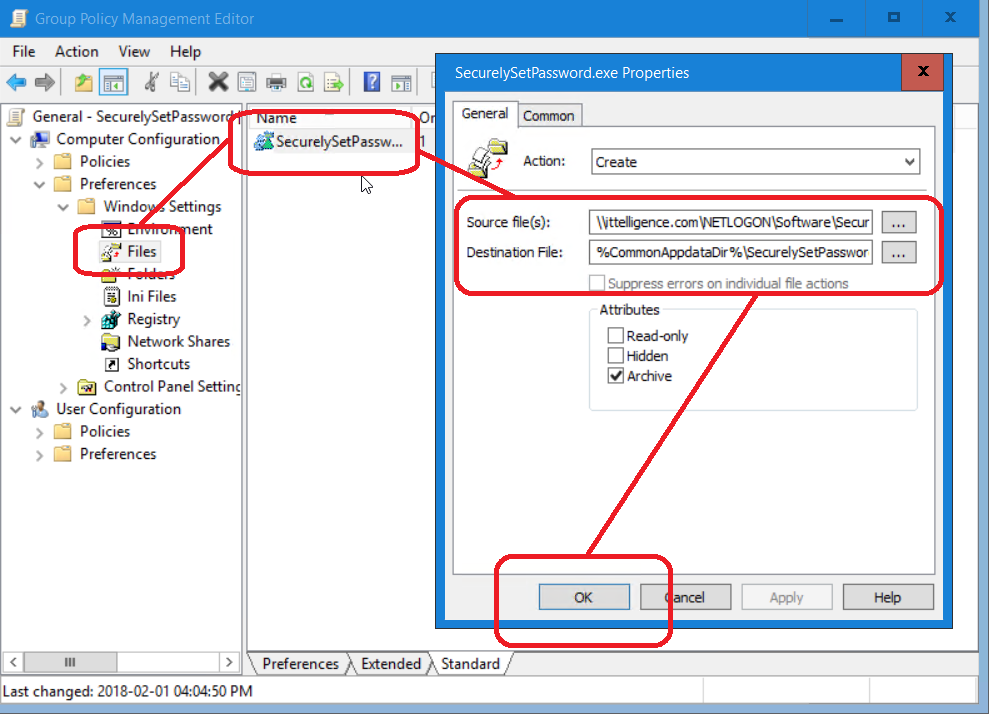
1) Download and extract
AdminGroups.zip (here is VirusTotal scan)
to a folder of your choice on the computer on which it will be scheduled to run.
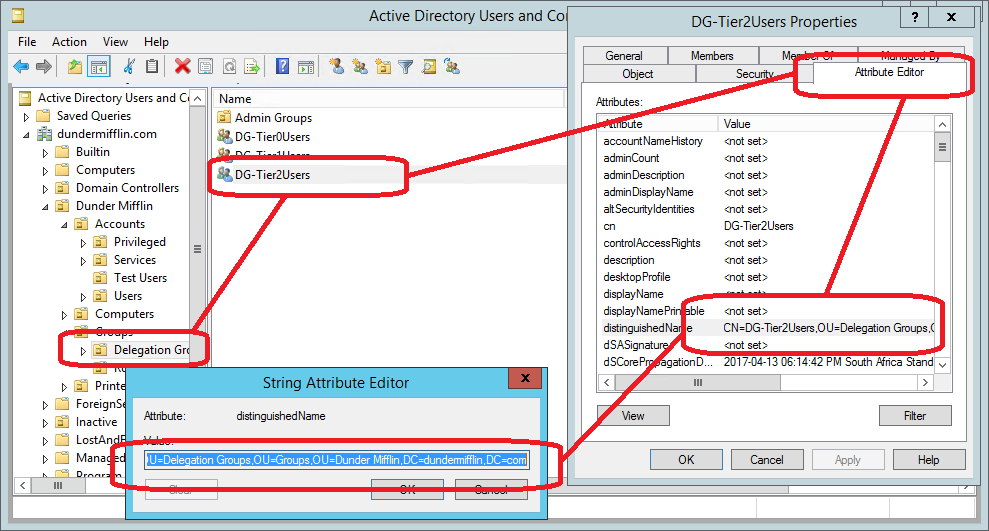
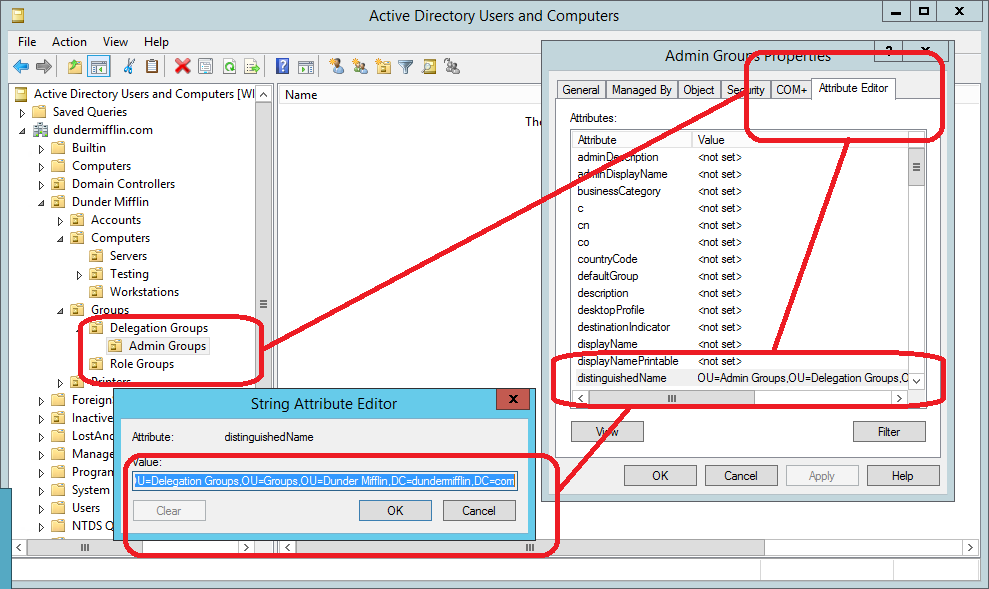
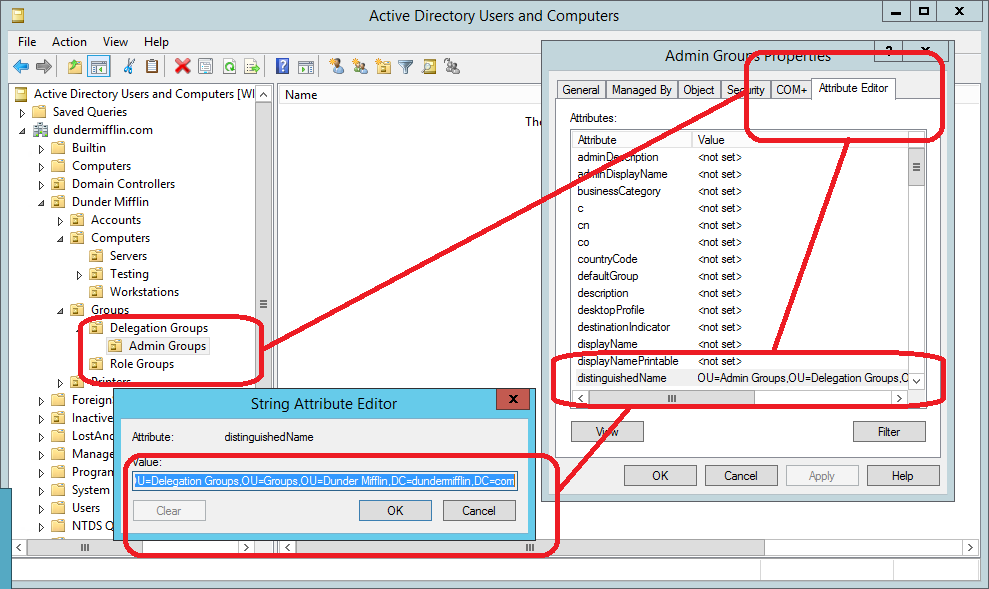
2) Create a location in Active Directory to create AD Local Admin groups in and record the distinguished name (DN).
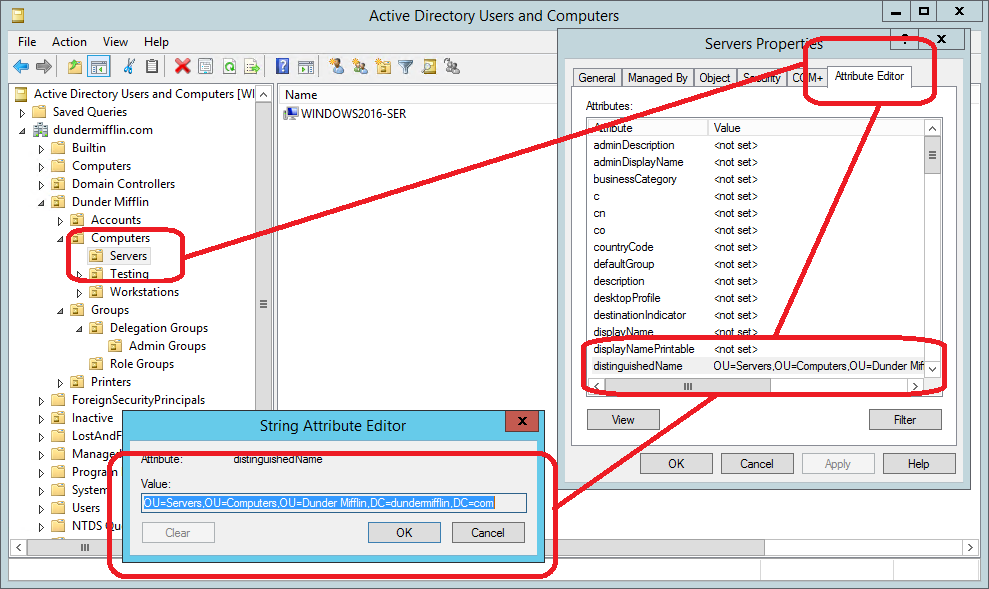
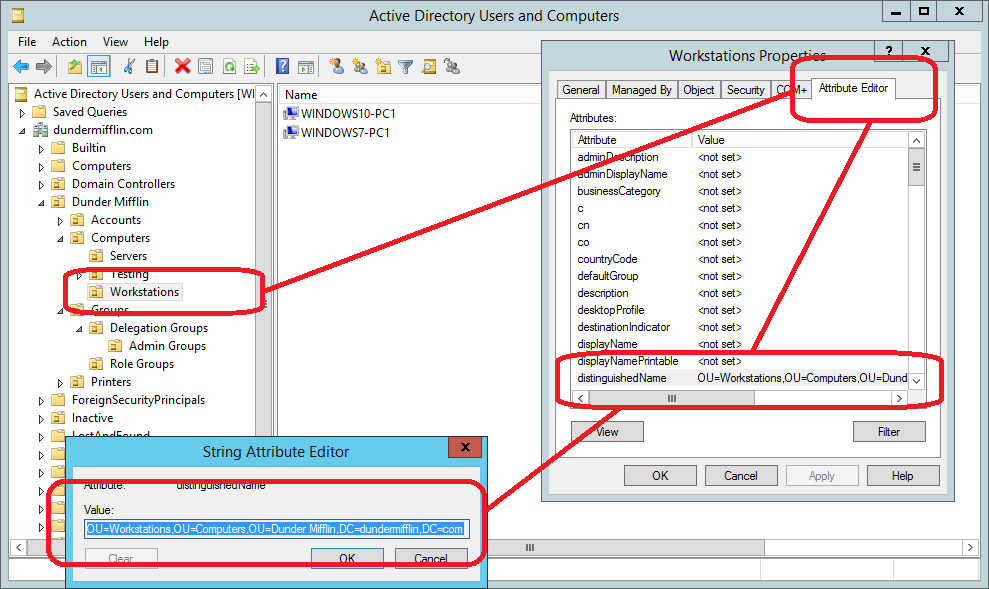
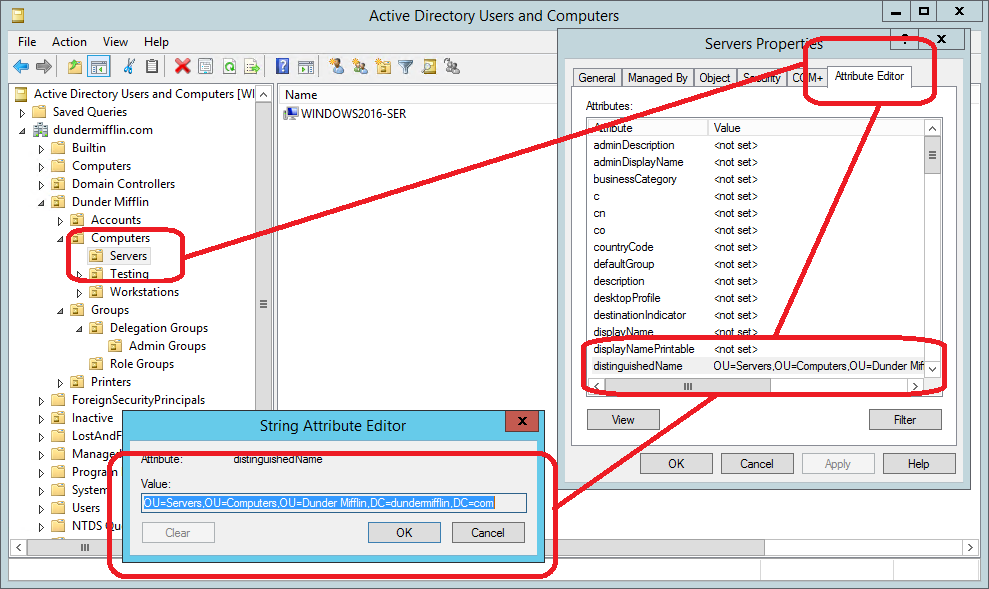
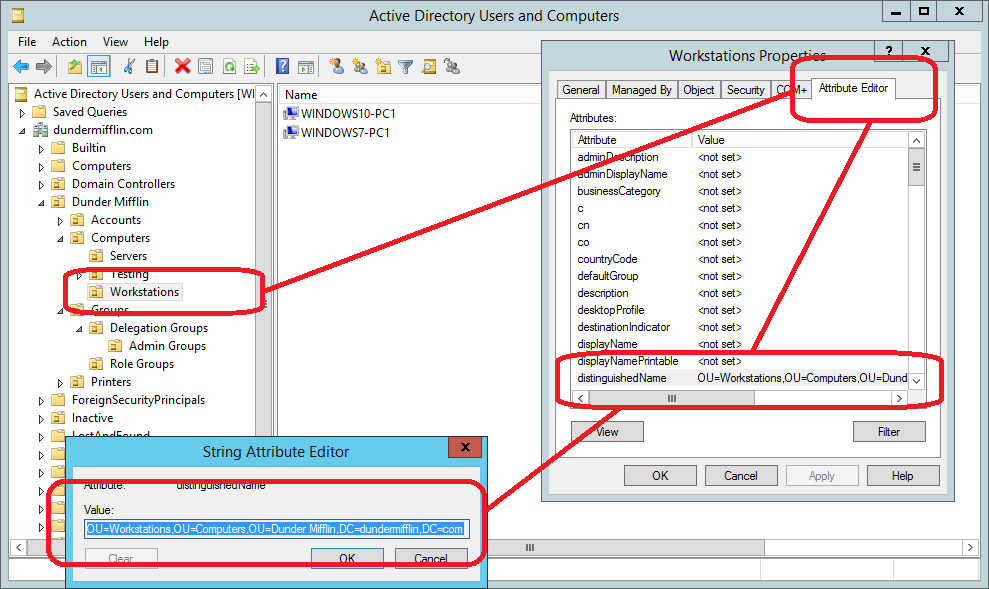
3) Record all the Computer OU’s distinguished name (DN) for the computers that AD Local Admin groups need to be created for. These can be workstations or servers but generally this in only done for servers.
4) Run
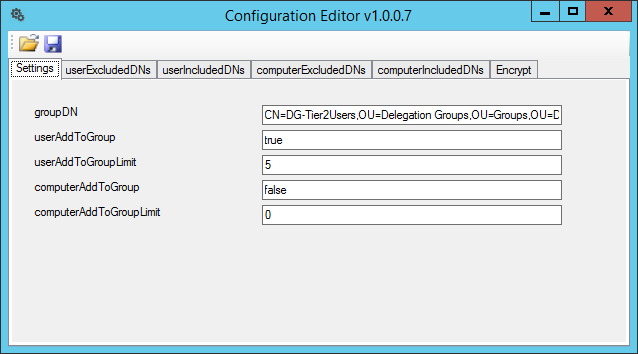
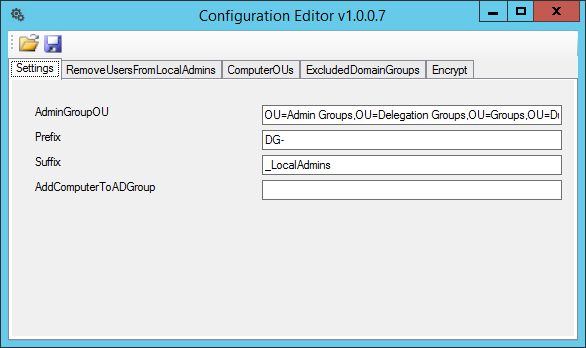
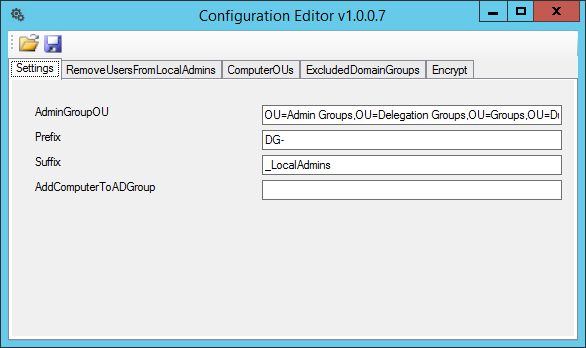
Configurator.exe (Configurator Editor).
All configuration is stored within the AdminGroups.ConsoleApp.exe.config file and can be either edited directly or with my Configuration Editor tool.
a) On the Settings tab, enter the Admin Group OU’s distinguished name (DN), recorded in Step 2.
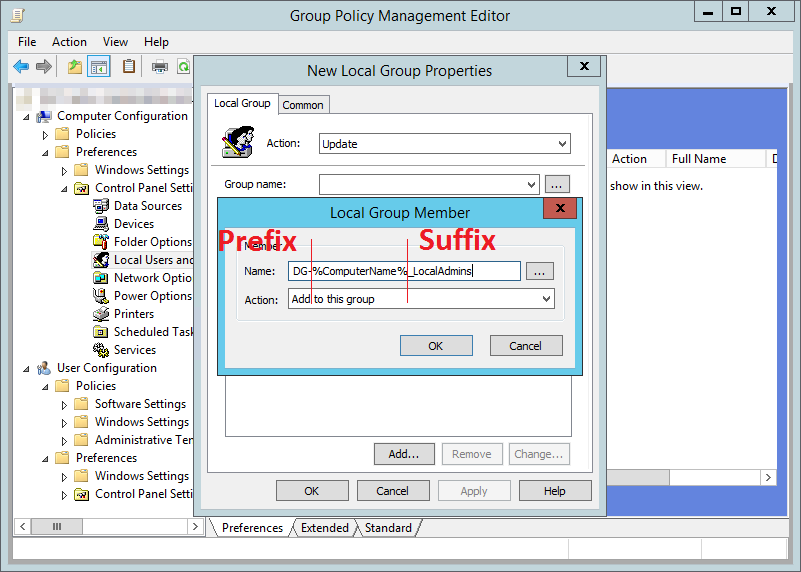
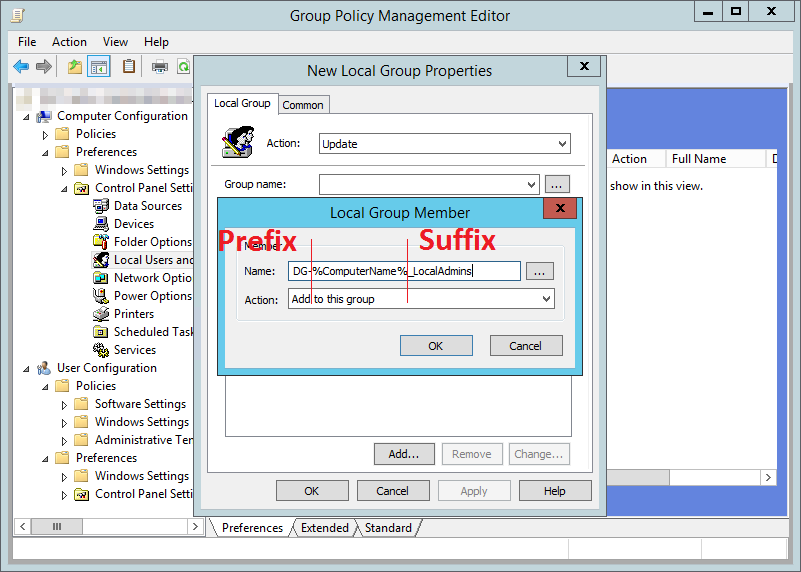
b) Enter the prefix that should be used when creating AD Local Admin Group.
c) Enter the suffix that should be used when creating AD Local Admin Group.
d) Optionally add a Group Name to add the computer account to on execution. This is useful if you want other policies to trigger or if you want to see process of the AdminGroups tool.
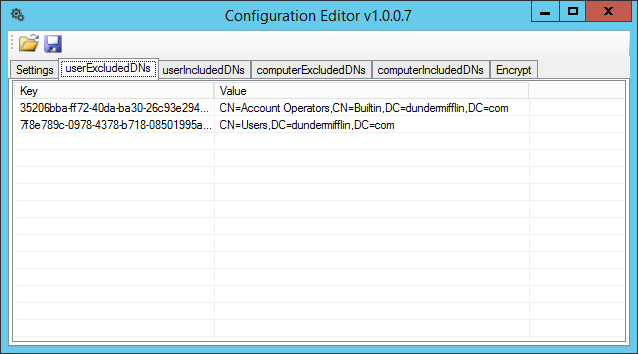
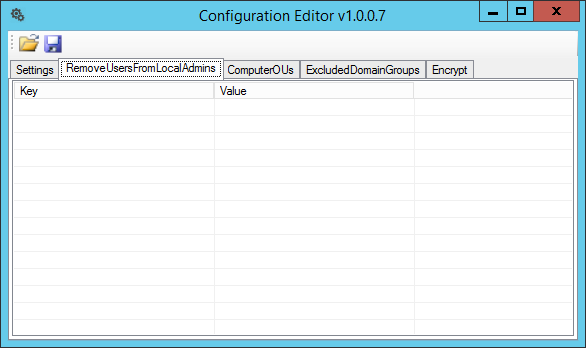
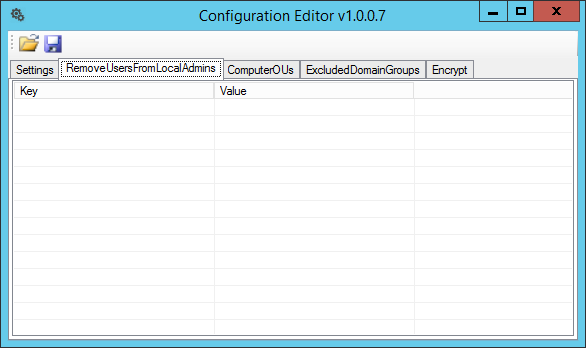
e) On the RemoveUsersFromLocalAdmins tab, enter usernames of local accounts that you want to automatically remove from the Local Administrators group.
Use this if redundant local user account with Administrators rights exist, perhaps accounts created as part of the imaging/build process. (Use +/-/Insert/Delete/Spacebar to manage entries.)
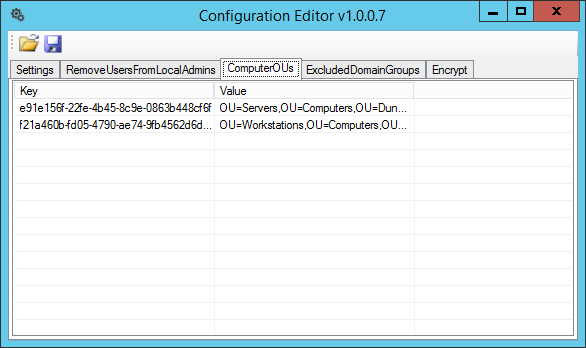
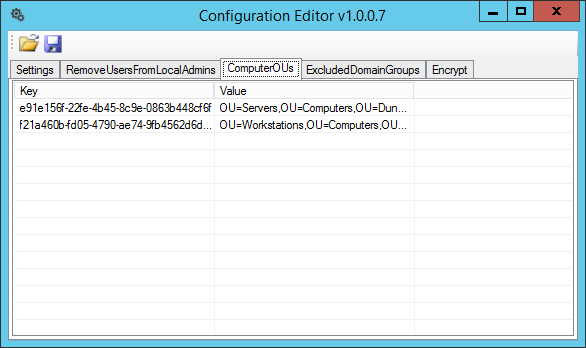
f) On the ComputerOUs tab, enter the Computer OU’s distinguished name (DN), recorded in Step 3. (Use +/-/Insert/Delete/Spacebar to manage entries.)
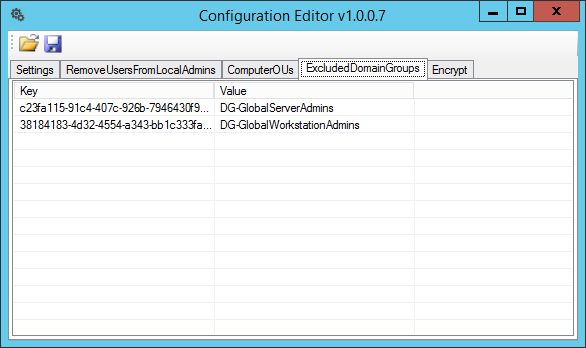
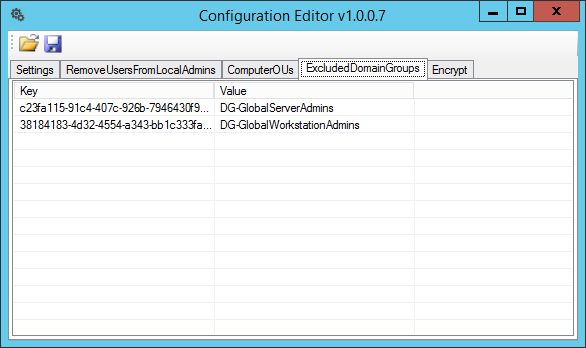
g) Add any groups that should not be automatically synced and removed from the AD Local Admins groups, for example, Global Admins. (Use +/-/Insert/Delete/Spacebar to manage entries.)
h) Save configuration file and close Configuration Editor.
This is how the XML file look for the above setting if you choose to edit it manually.
<?xml version="1.0" encoding="utf-8"?>
<configuration>
<configSections>
<section name="RemoveUsersFromLocalAdmins" type="System.Configuration.NameValueSectionHandler" />
<section name="ComputerOUs" type="System.Configuration.NameValueSectionHandler" />
<section name="ExcludedDomainGroups" type="System.Configuration.NameValueSectionHandler" />
</configSections>
<ComputerOUs>
<add key="e91e156f-22fe-4b45-8c9e-0863b448cf6f" value="OU=Servers,OU=Computers,OU=Dunder Mifflin,DC=dundermifflin,DC=com" />
<add key="f21a460b-fd05-4790-ae74-9fb4562d6d0b" value="OU=Workstations,OU=Computers,OU=Dunder Mifflin,DC=dundermifflin,DC=com" />
</ComputerOUs>
<RemoveUsersFromLocalAdmins />
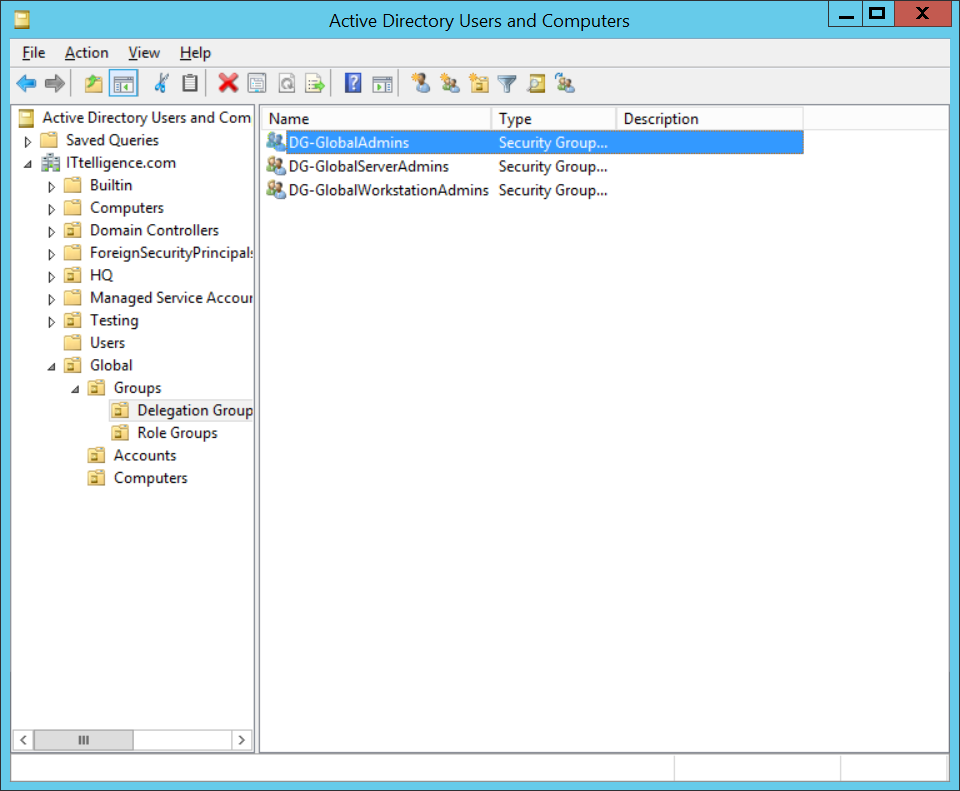
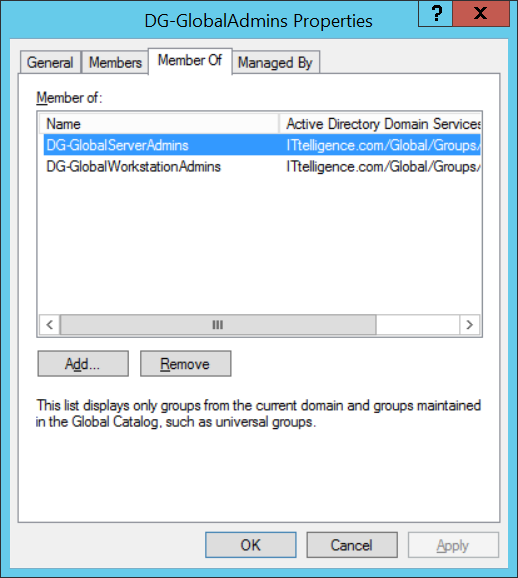
<ExcludedDomainGroups>
<add key="c23fa115-91c4-407c-926b-7946430f93df" value="DG-GlobalServerAdmins" />
<add key="38184183-4d32-4554-a343-bb1c333faef3" value="DG-GlobalWorkstationAdmins" />
</ExcludedDomainGroups>
<appSettings>
<add key="AdminGroupOU" value="OU=Admin Groups,OU=Delegation Groups,OU=Groups,OU=Dunder Mifflin,DC=dundermifflin,DC=com" />
<add key="Prefix" value="DG-" />
<add key="Suffix" value="_LocalAdmins" />
<add key="AddComputerToADGroup" value="" />
</appSettings>
<startup>
<supportedRuntime version="v4.0" sku=".NETFramework,Version=v4.5" />
</startup>
</configuration>
i) Schedule AdminGroups.ConsoleApp.exe to run one every day. Remember to set the running account to an account with rights
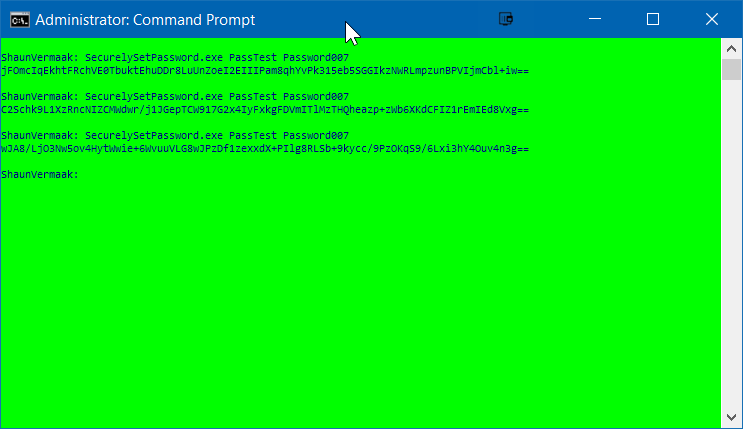
Demo Execution
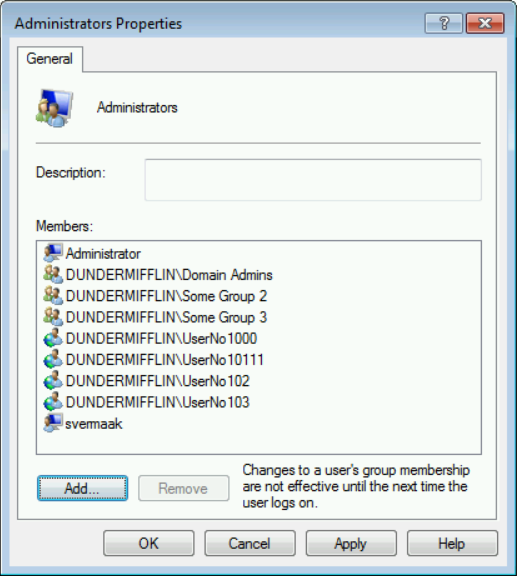
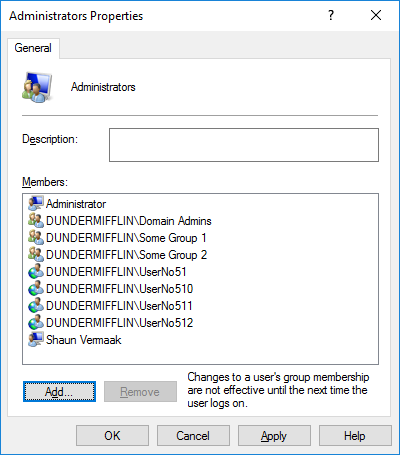
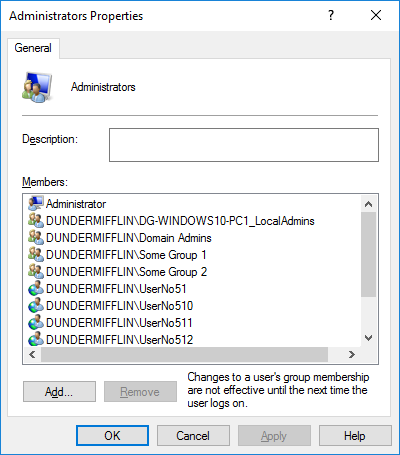
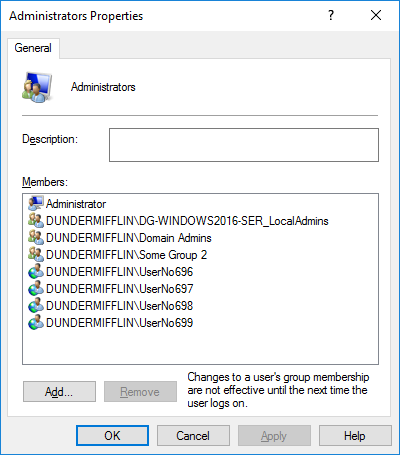
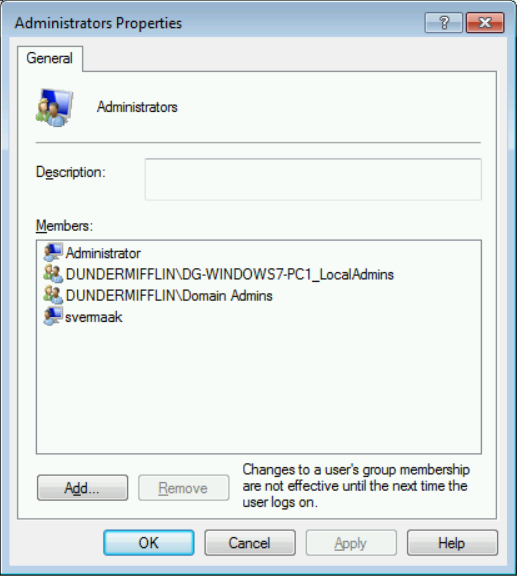
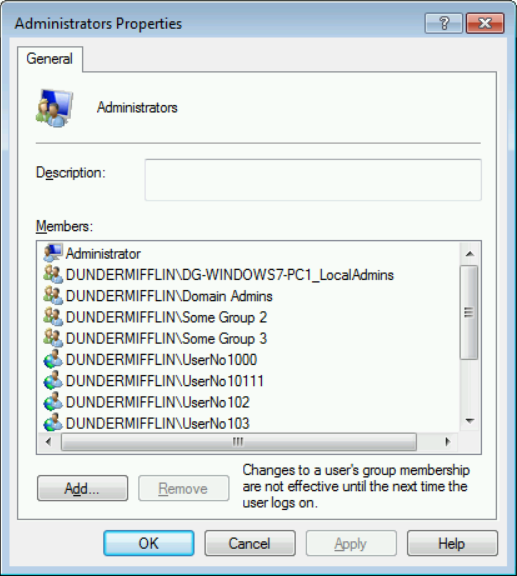
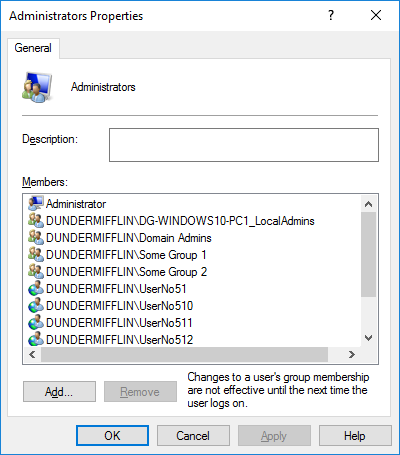
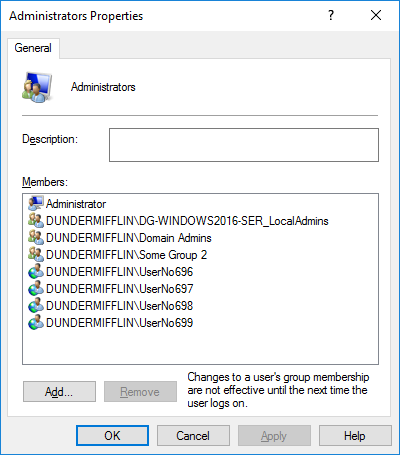
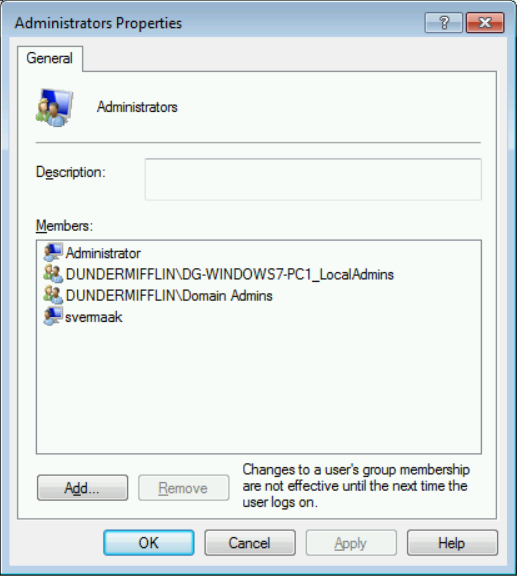
1) Below is screenshots of my three demo computers’ Local Administrators groups pre-execution.
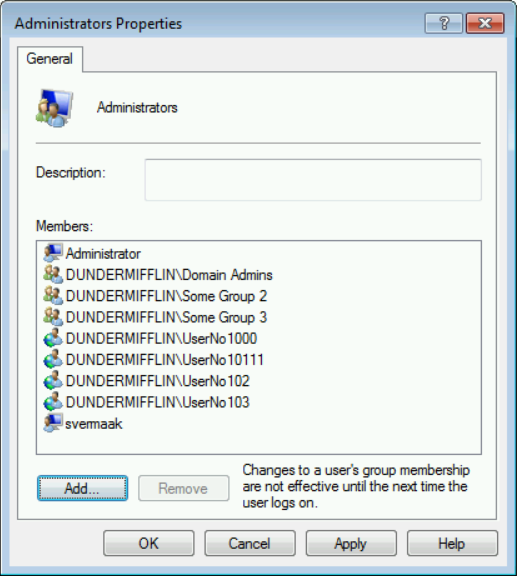
Windows 7 original Local Administrators Group
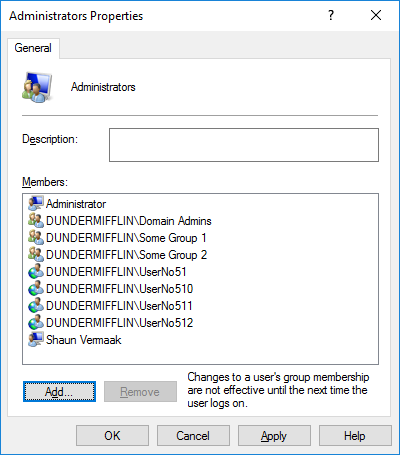
Windows 10 original Local Administrators Group
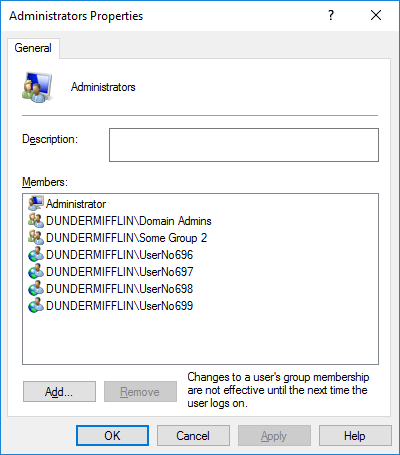
Windows 2016 original Local Administrators Group
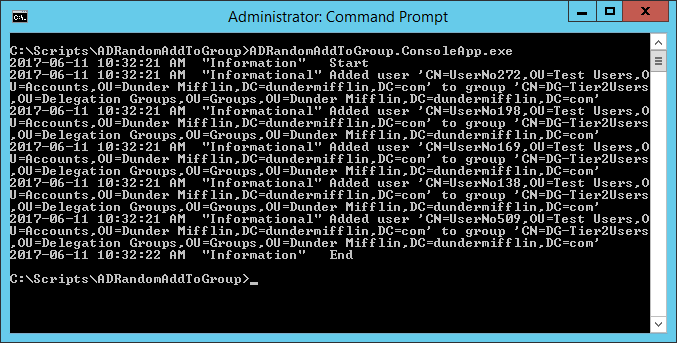
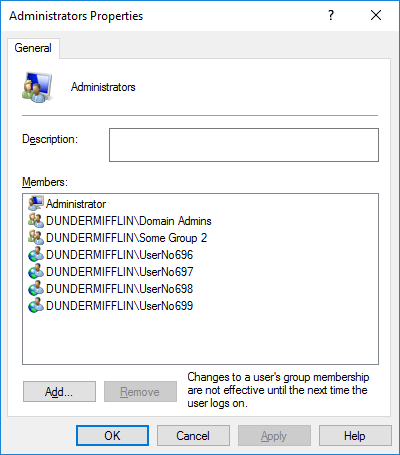
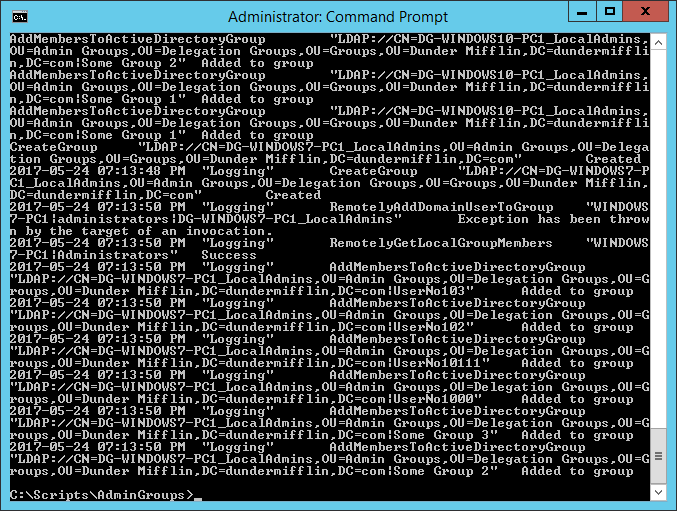
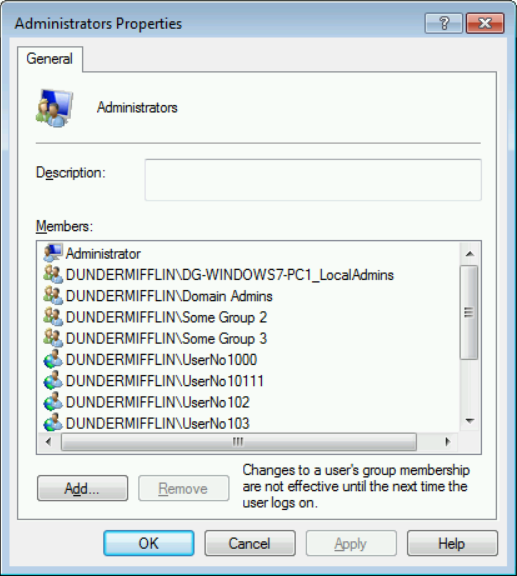
2) Below are screenshots of AdminGroup output and my three demo computers’ Local Administrators groups after first execution
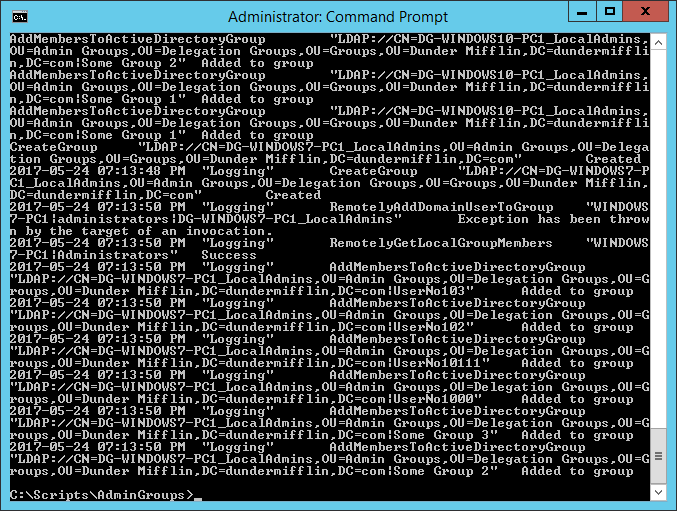
AdminGroups output after first execution
Windows 7 Local Administrators Group after first execution
Windows 10 Local Administrators Group after first execution
Windows 2016 Local Administrators Group after first execution
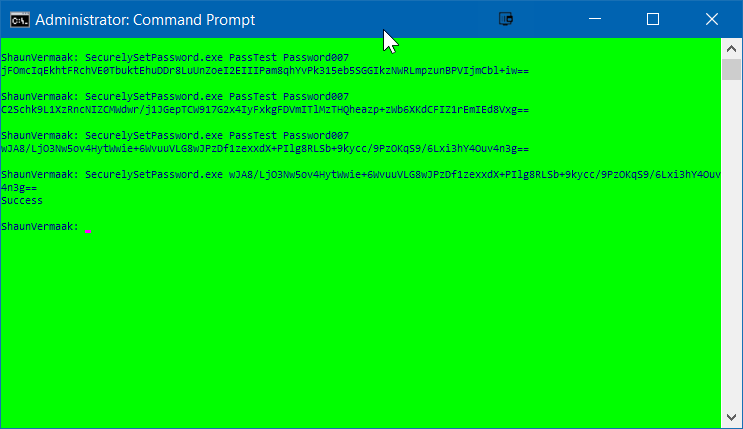
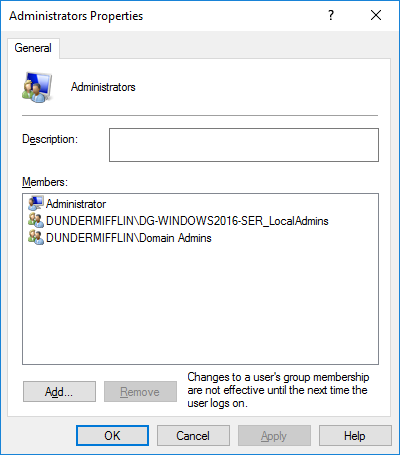
3) Below is screenshots of AdminGroup output and my three demo computers’ Local Administrators groups after second execution.

AdminGroups output after second execution
Windows 7 Local Administrators Group after second execution

Windows 10 Local Administrators Group after second execution
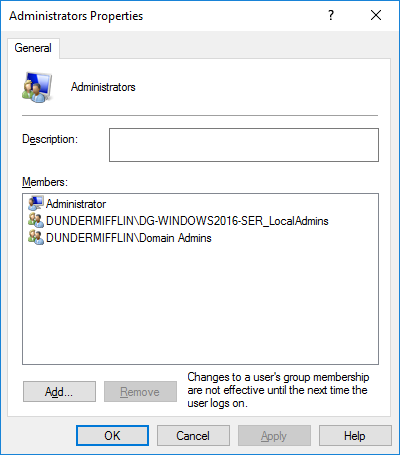
Windows 2016 Local Administrators Group after second execution
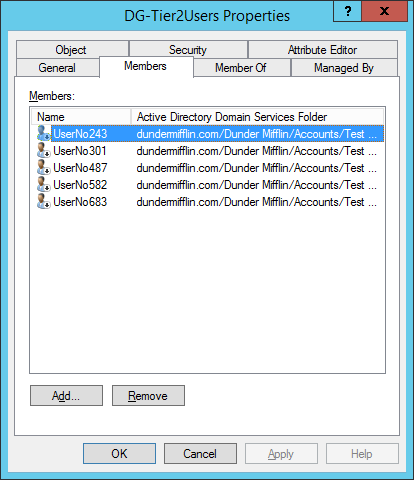
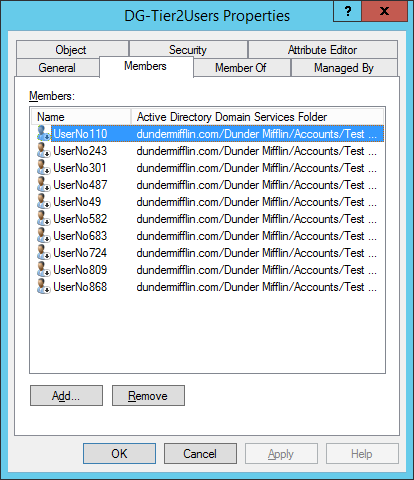
Where did members go? They are now safely within the AD Local Admins groups.

Windows 7 AD Local Admins Group
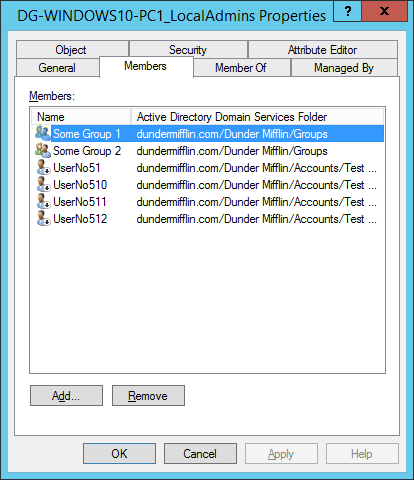
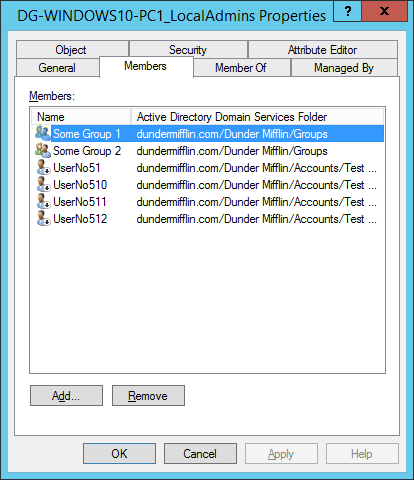
Windows 10 AD Local Admins Group
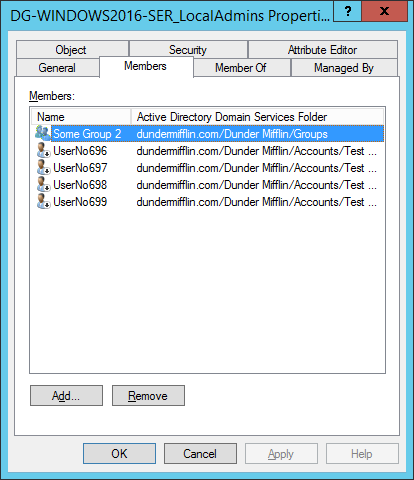
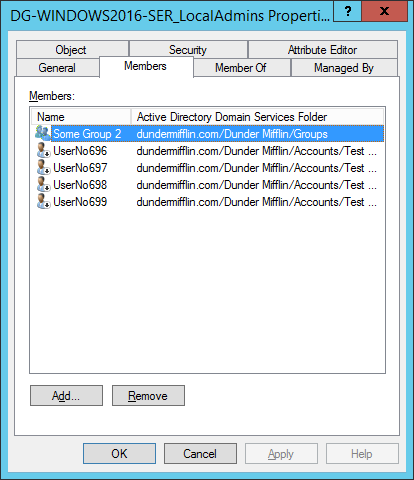
Windows 2016 AD Local Admins Group
Code
Here is the section in code that manages the AD Local Admin Groups.
public static bool CreateAdminGroup(string DomainName, Models.Computer Computer, string AdminGroupOU, string AdminGroupName, List < string > ExcludedDomainGroups, out string Message) {
Message = "";
string message = "";
try {
//If this fails, no point in continueing
if (ActiveDirectory.CreateActiveDirectoryGroup(AdminGroupOU, AdminGroupName, out message)) {
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
//If this fails, no point in continueing
if (ActiveDirectory.RemotelyAddDomainGroupToLocalGroup(Computer.ComputerName, DomainName, AdminGroupName, "administrators", out message)) {
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
List < Models.GroupMember > groupMembers = new List < Models.GroupMember > ();
//If this fails, no point in continueing
if (ActiveDirectory.RemotelyGetLocalGroupMembers(Computer.ComputerName, "Administrators", true, false, ref groupMembers, out message)) {
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
foreach(Models.GroupMember groupMember in groupMembers) {
//Handle excluded domain groups
if ((!AdminGroupName.EndsWith(groupMember.GroupMemberName)) && (groupMember.GroupMemberName != "Domain Admins") && (!ExcludedDomainGroups.Contains(groupMember.GroupMemberName))) {
if (ActiveDirectory.AddMemberToActiveDirectoryGroup(AdminGroupOU, AdminGroupName, groupMember.GroupMemberName, out message)) {
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
if (message.EndsWith("Group already exists")) {
ActiveDirectory.RemotelyRemoveDomainGroupFromLocalGroup(Computer.ComputerName, DomainName, groupMember.GroupMemberName, "administrators", out message);
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
}
} else {
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
}
}
}
} else {
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
}
} else {
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
}
} else {
//Add command output to return message
Message = Message + System.Environment.NewLine + message;
}
return true;
} catch (Exception ex) {
Message = Message + System.Environment.NewLine + ex.Message;
return false;
}
}
Conclusion
Using this process, or one similar will give better visibility on existing users with Local Administrators permissions and the ability to better manage them.