INTRODUCTION
This is a process I use whenever I get an “Access Denied” message. One example of this is when I do not have access to SQL Server directly, only administrative rights to the actual server.
PROCESS
1) Download PsExec which is part of the PsTools suite
2) Extract PsTools.zip to a convenient location. I usually copy PsExec.exe to the System32 folder. This allows PsExec.exe to be executed from any folders without specifying the full path.
3) Execute the following command
PsExec.exe -s -i -d CMD.exe
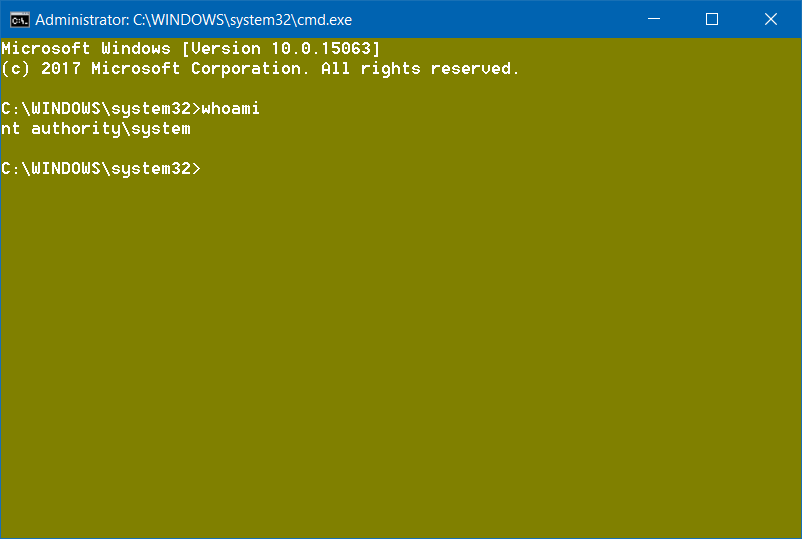
4) From within this new command prompt, everything you open will open as the SYSTEM account.
EXAMPLES
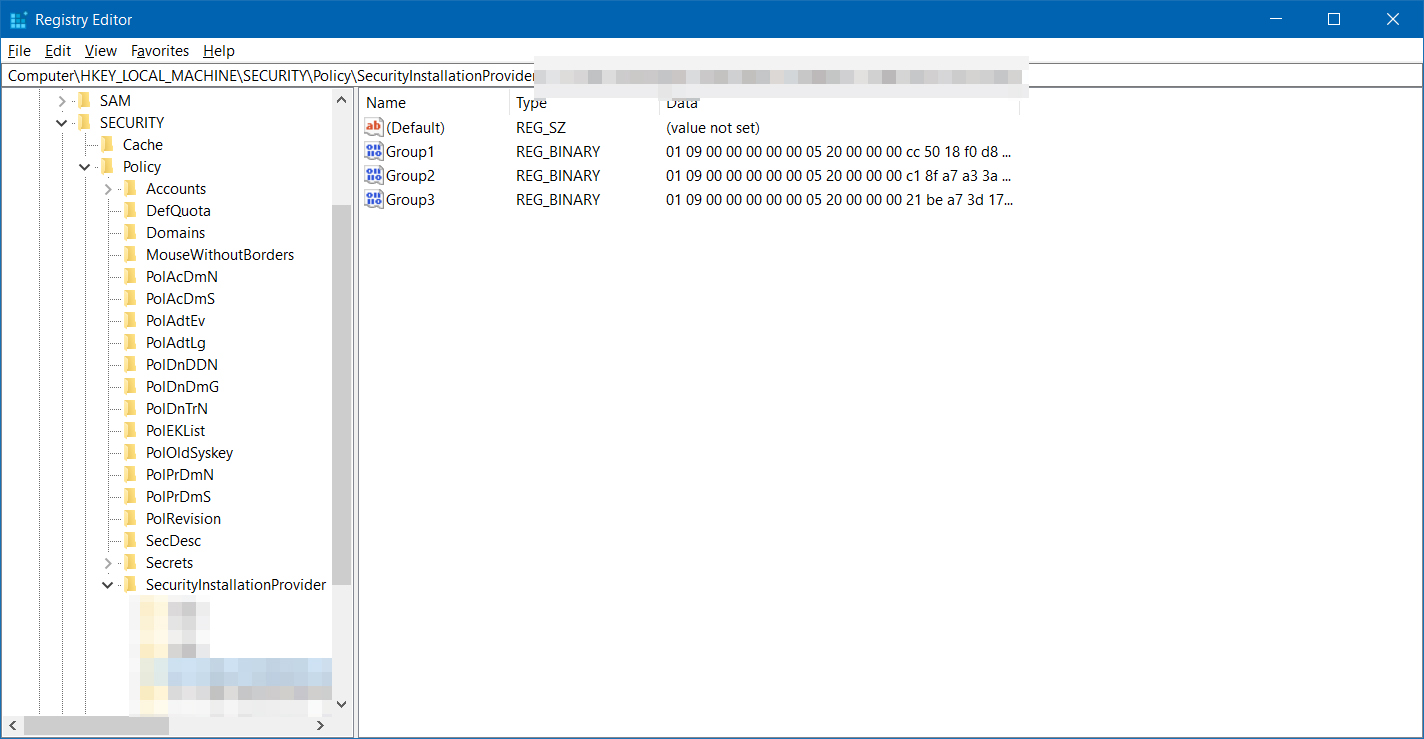
Viewing NT Secrets
Open Regedit.exe and you will be able to see content of HKEY_LOCAL_MACHINE\SECURITY
- This allows you to view passwords that were stored as NT Secrets
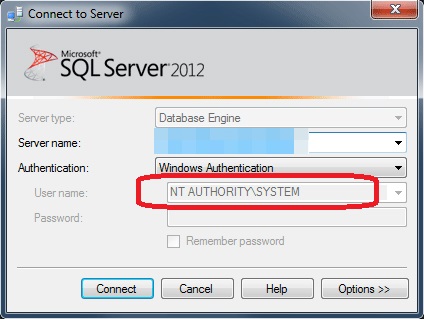
Opening SQL Server Management Studio as SYSTEM
Open SQL Management Studio and you will be able to log on with SYSTEM
- This allows you to access SQL without directly having been granted SQL right yet you have administrative rights to SQL Server
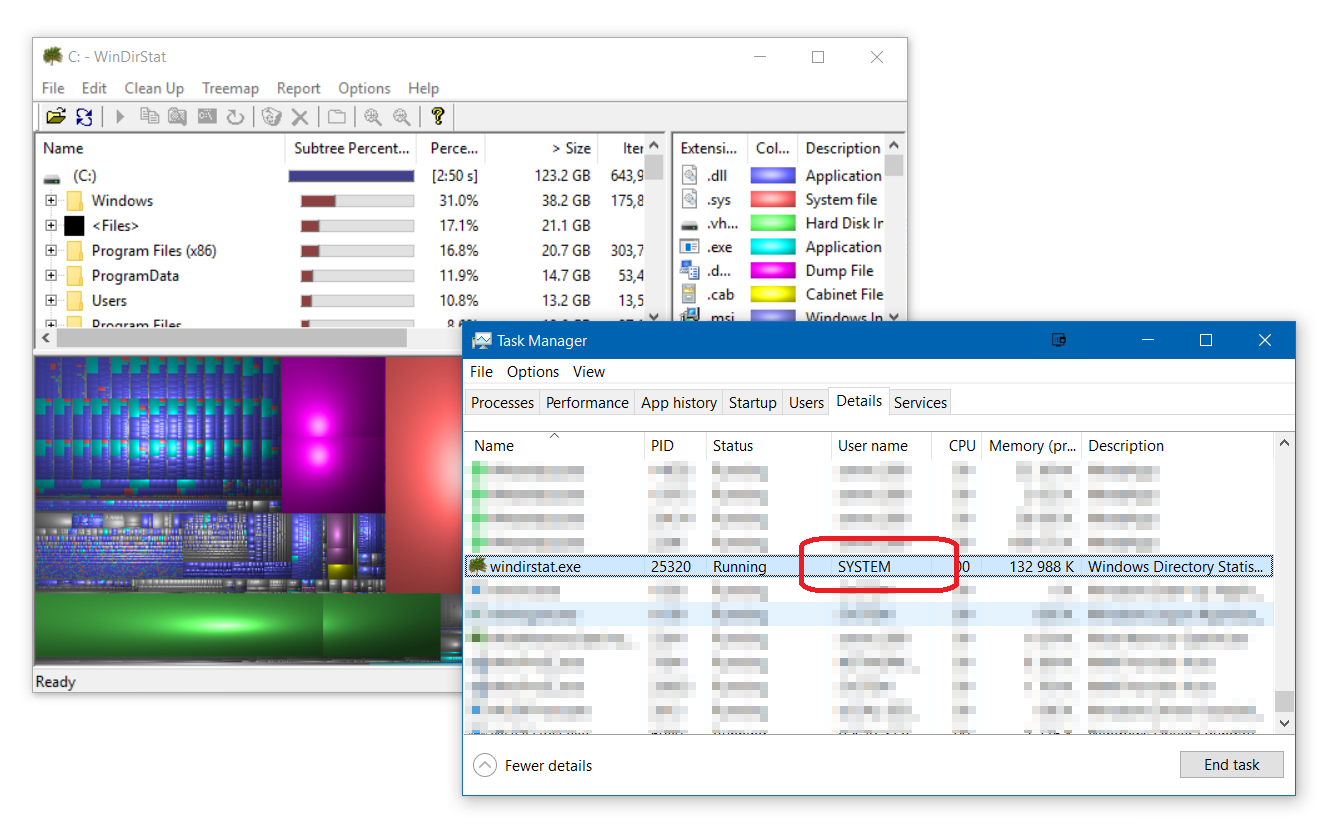
You will be able to browse to any folder that only allows SYSTEM account
- You can export permissions with SetACL/ICACLS to folders that administrators group might have been removed on
- Kill processes that give error Access Denied when you try to terminate it with normal Administrator rights
WinDirStat/TreeSize etc.
Running something like TreeSize as SYSTEM will actually give you a better view and understanding of what is using space because you will get less access denials
Some others…
- Simulate GPO start scripts
- Simulate GPO based MSI installation
- Diagnose why scheduled tasks that run as SYSTEM don’t run as intended
- Start/stop protected services
CONCLUSION
Using this process, (or one similar) will allow you to start processes as the SYSTEM account allowing you to access parts of files system, registry and application not accessible with normal Administrative rights.